El blog de la EnBITCon
Cambia ahora y ahorra – Promoción Sophos 1U/2U para nuevos clientes
¿Estás pensando en modernizar tu infraestructura de firewall existente? Ahora es el momento perfecto
Puntos de acceso al aire libre – Soluciones Wi-Fi robustas para uso en exteriores
A medida que la digitalización se extiende, también en exteriores se necesita Wi-Fi confiable — ya sea para almacenes, centros logísticos o similares
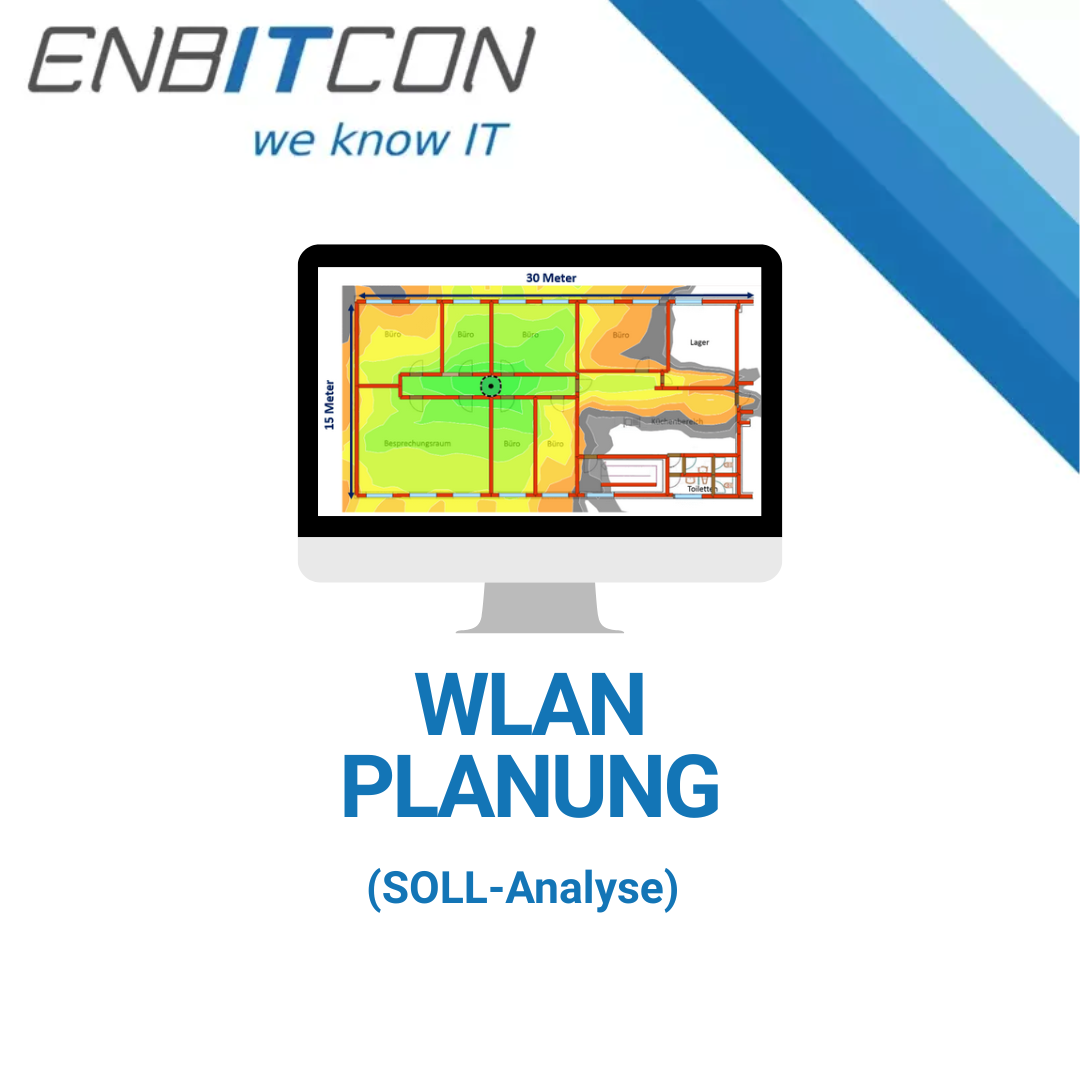
Cobertura WLAN en forma de planificación WLAN digital
En principio, la mera planificación WLAN para un nuevo edificio u otra infraestructura puede ser suficiente para garantizar una funcionalidad WLAN sin problemas sin llevar a cabo una medición de referencia en forma de iluminación WLAN.
Sophos Firewall v21.5: Nuevos estándares en seguridad de redes y facilidad de uso
Con el lanzamiento de Sophos Firewall v21.5, Sophos vuelve a marcar la pauta en seguridad de redes
INFORME OPENVAS de Greenbone: Análisis central de vulnerabilidades para infraestructuras IT modernas
Con el INFORME OPENVAS de Greenbone, obtiene una visión central de todas las vulnerabilidades de su infraestructura
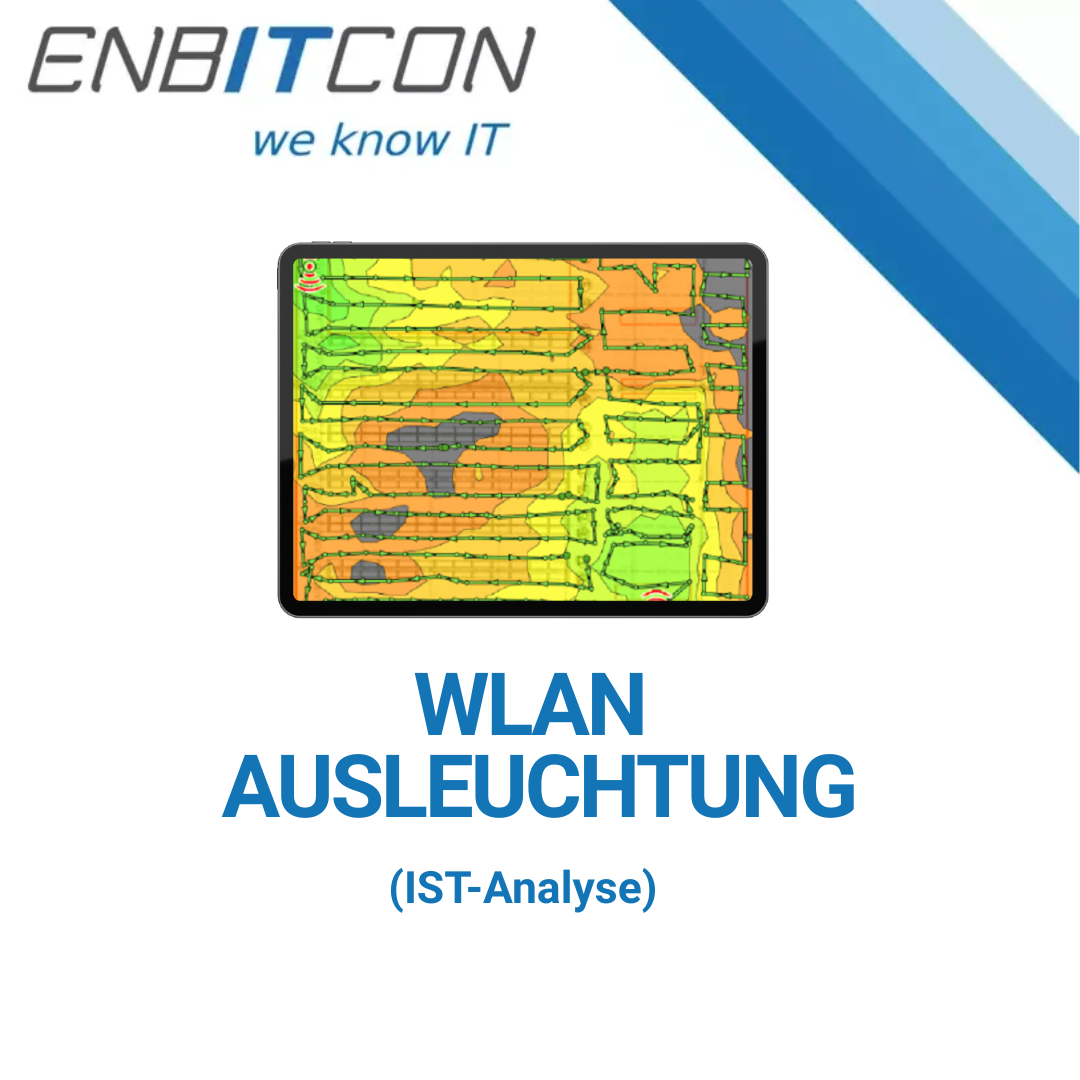
¿Qué es la iluminación WLAN?
Por cobertura WLAN se entiende una medición de referencia de una infraestructura WLAN que ya se ha puesto en funcionamiento ...
¿Qué es la planificación WLAN?
La planificación WLAN es básicamente un concepto para la funcionalidad de la LAN inalámbrica en un edificio, una sección u otra zona, que también puede ser una zona exterior, por ejemplo.
Monitoreo de la Web Oscura – Por qué es importante saber si los datos de su empresa están siendo comerciados
Con el Monitoreo de la Web Oscura, puede detectar información comprometida tempranamente – antes de que ocurra un daño real